Distributed denial of service (DDoS) attacks are unfortunately common in the world of internet security. Here is a description of the most common types and how to protect against them: Volumetric Attacks: These attacks flood a network with an enormous volume of traffic, often generated by a...
Common Types of SQL Injection Attacks Classic Injection: The attacker inserts or injects an SQL query through the application's data input, which is then executed by the database management system. This can allow reading, modifying, or deleting data. Error-Based Injection: Exploits error m...
What is an XSS Attack? An XSS (Cross-Site Scripting) attack occurs when an attacker manages to inject malicious code, usually JavaScript, into a website that other users will execute unknowingly. This differs from other web attacks because it exploits the vulnerabilities of the site's users r...
"Man In The Middle" (MITM) attacks "Man In The Middle" (MITM) attacks are a significant concern in the world of cybersecurity. These attacks occur when an attacker intercepts communication between two parties without their consent, often aiming to steal sensitive information o...
Understanding and Countering Phishing Attacks Introduction Phishing, a form of cyberattack, remains a persistent threat in the digital world. These attacks aim to deceive users into divulging sensitive information. Understanding the techniques used by hackers and knowing how to protect onese...
Essential Practices and Advantages for Businesses 1. Introduction to SEO Search Engine Optimization (SEO) encompasses a set of practices aimed at increasing a website's visibility and ranking in search engine results pages. With the constant evolution of search algorithms, SEO has become a cr...
The Importance of SMO for Modern Businesses 1. Introduction to SMO (Social Media Optimization) and Its Role in Today’s Digital Landscape Social Media Optimization (SMO) is a crucial strategy in today's digital world. It involves using social networks like Facebook, Twitter, Li...
In today's competitive digital arena, SEA (Search Engine Advertising) is an invaluable tool for increasing a company's visibility. This article delves into the details of SEA, lists the essential tools for success, and identifies common pitfalls to avoid. What is SEA? SEA i...
Introduction to No Code and Low Code Development No Code and Low Code development are revolutionary approaches to software development that have gained popularity in recent years. They aim to simplify the process of creating web and mobile applications by reducing the need for manual coding. ...
Introduction to Custom Typography This first paragraph will introduce custom typography, explaining its importance in web design and how it has evolved over time. It will highlight how well-chosen typography can influence a brand's identity and the user experience. The History of Typogra...
Introduction to Animations and micro-interactions Animations and micro-interactions have become essential elements in modern web design. They offer a more engaging and interactive user experience, thus enhancing the usability of a website. Understanding Animations Animations involve ...
Integration with Desktop Software Microsoft 365 offers seamless integration with its established desktop applications like Word, Excel, and PowerPoint. For businesses already heavily reliant on these tools for their daily operations, choosing Microsoft 365 allows for a smooth transition to the ...
The Importance of Google Analytics 4 for Businesses In today’s digital world, understanding user behavior on a website is crucial for a business's success. Google Analytics 4 (GA4) stands at the forefront of this analytics, offering in-depth insights into user interactions. This artic...
DomainTools is a well-regarded platform in the cybersecurity field, offering an extensive range of services centered around internet domain analysis and research. The flagship service of DomainTools, accessible via https://whois.domaintools.com/, allows users to perform in-depth WHOIS searches. ...
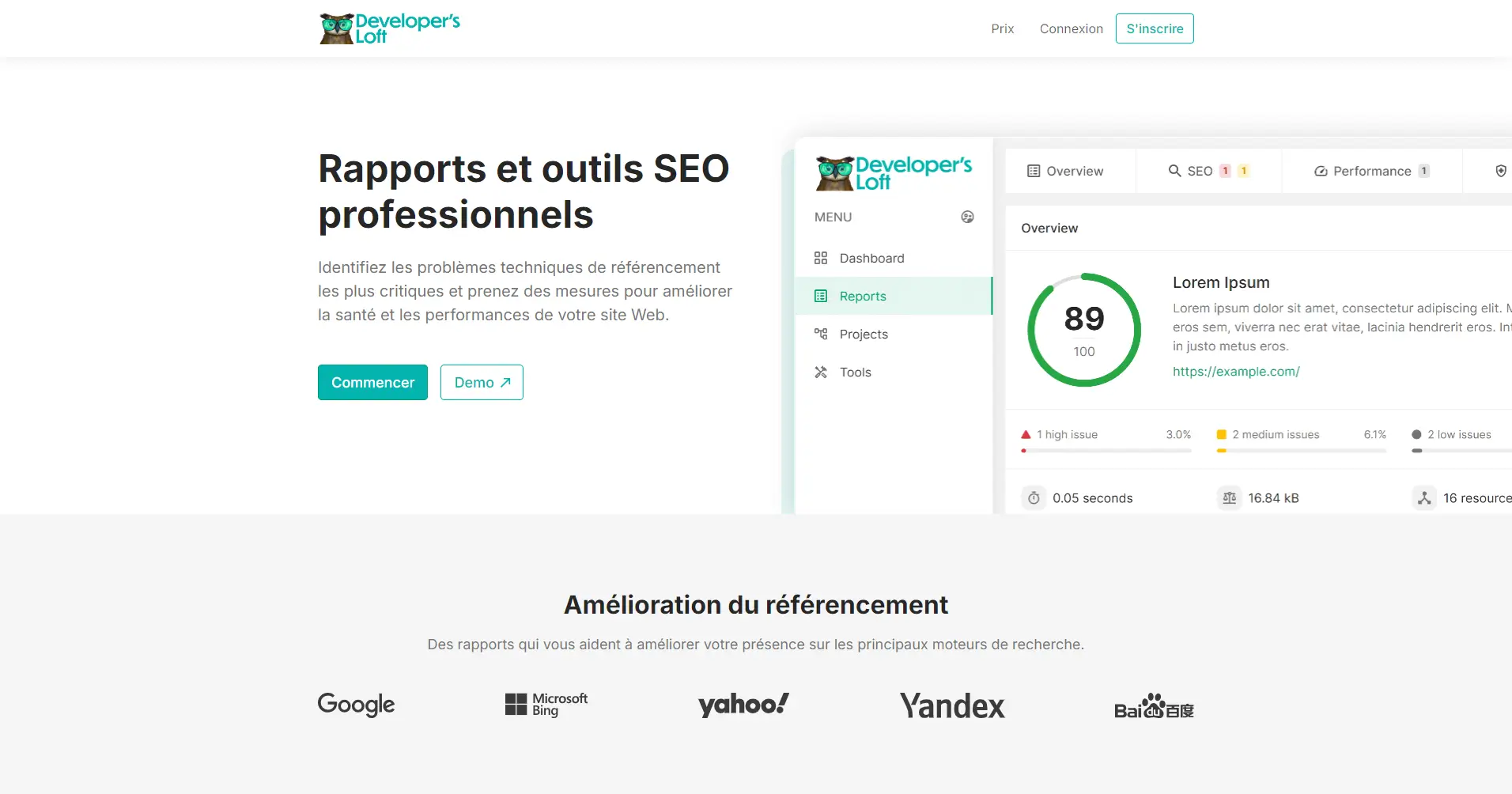
Developer's Loft is a comprehensive platform designed for improving website SEO through detailed reports and tools. It offers solutions for identifying and addressing technical SEO issues, enhancing website performance, and ensuring security. The service provides a complete suite of tools f...
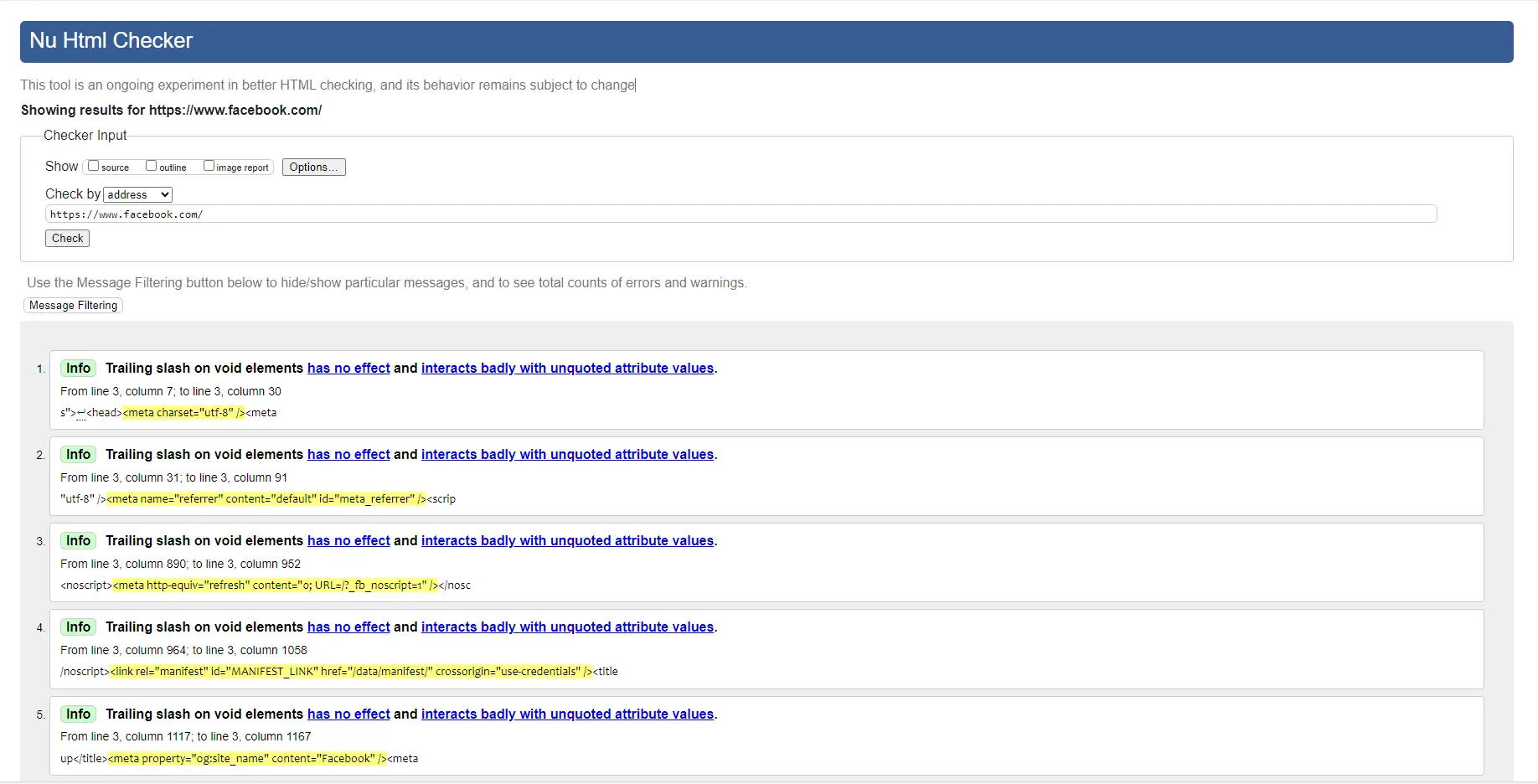
The Nu HTML Checker service, available at https://validator.w3.org/nu/, is a crucial tool for web developers who aim to ensure their sites comply with web standards. Developed by the World Wide Web Consortium (W3C), this online tool allows for the validation of HTML and XHTML documents to ensure t...
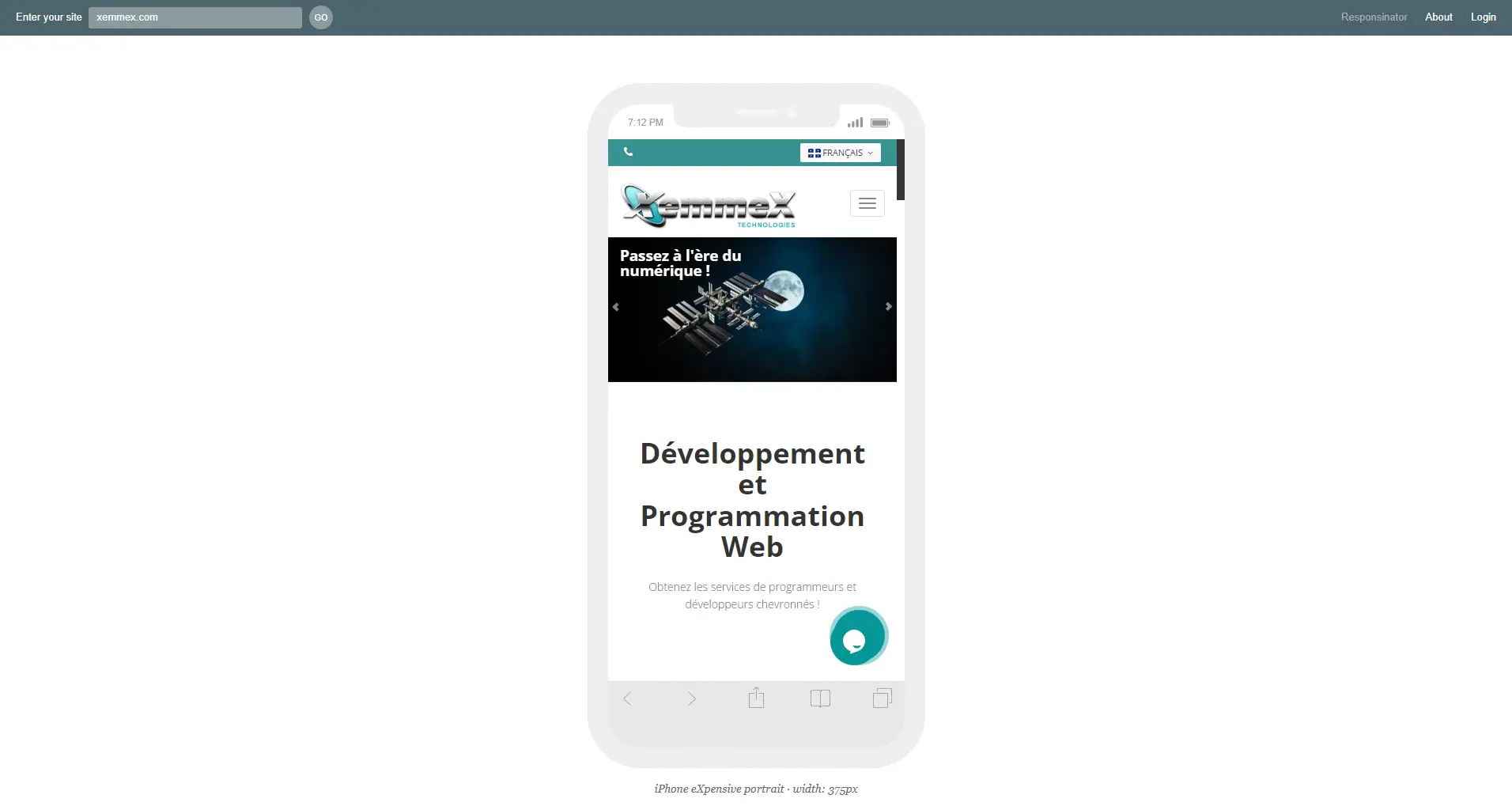
Responsinator is an online tool designed to help web developers and designers quickly visualize how their websites perform on various mobile devices. In an era where mobile browsing accounts for a significant portion of internet traffic, providing an optimal user experience across all device types h...
A Revolution Underway In today's digital world, speed and efficiency are paramount. Developers and web designers are constantly on the lookout for new methods to improve user experience by optimizing website performance. One key aspect of this quest for optimization is the choice of image a...
Creating a logo or a trademark is a crucial step for any business looking to stand out in the market. This creative process, while exciting, requires meticulous planning and deep reflection. Here’s an overview of the steps to follow and the pitfalls to avoid when developing a logo that embod...
In my twenty years of experience in data management, I’ve often noticed a recurring pattern among entrepreneurs: as their business grows, managing data becomes a real headache. Fragmented information, duplicated processes, and the absence of a centralized structure often lead to results that...
 English
English
 Français
Français